Rethink what you share – this is your organisation’s greatest unmanaged security risk.
LinkedIn has been marketed to us as a professional community – a place to build careers, share expertise, and forge meaningful business relationships. For many, it has delivered on that promise. But there is a darker dimension to this platform that almost nobody in mainstream business is talking about: LinkedIn is also one of the most powerful reconnaissance tools available to hackers, state-sponsored cyber threat actors, and organised criminal groups – and the information you are willingly posting is fuelling their attack campaigns.
LinkedIn Is an OSINT Goldmine
Open Source Intelligence (OSINT) refers to the collection and analysis of information from publicly available sources to support intelligence and, increasingly, attack operations. It is not exotic or technically demanding; it is methodical, patient, and devastatingly effective. And LinkedIn is, without question, one of the richest OSINT resources on the internet.
Security professionals, penetration testers, and intelligence agencies explicitly classify professional networking sites such as LinkedIn as primary targets for social media intelligence gathering (SOCMINT) – a subset of OSINT. As experts at PwC UK’s threat intelligence practice have noted, these platforms can provide extensive data that can be weaponised and used in phishing campaigns or for performing targeted password spray attacks.
When a determined attacker – whether that be an opportunistic cybercriminal, an organised ransomware group, or a nation-state actor (think APT32, etc…) – begins scoping a target organisation, LinkedIn is almost invariably their first port of call. Why? Because in a matter of hours, it can reveal the following with extraordinary precision:
- The complete organisational chart:
Who reports to whom, which teams exist, who has just joined, who is about to leave.
→
- Technology stack and security posture:
New IT projects, security programmes, compliance initiatives, and tooling – frequently posted proudly by employees and their managers.
→
- Third-party partnerships and suppliers:
Partnership announcements that immediately expose new, potentially less-hardened attack vectors.
→
- Personal details and behavioural patterns:
Work anniversaries, new roles, travel schedules, personal email addresses, and phone numbers – all building blocks for sophisticated social engineering.
→
- Weakest-link personnel:
Junior administrators, newly hired staff, or individuals publicly voicing frustration with their employer – all prime targets for manipulation.
Trend Micro research has explicitly described LinkedIn as “an optimal platform to gather information on potential targets and for initial reconnaissance,” noting that its focus on professional, work-related data is precisely what makes it so attractive to malicious actors. Advanced Persistent Threat (APT) group Lazarus – a North Korean state-sponsored hacking organisation – has been documented using LinkedIn for cybercriminal and espionage operations.
The Supply Chain Blindspot
One of the most under-appreciated risks introduced by uninhibited LinkedIn activity is supply chain exposure. When your organisation publicly announces a new partnership with a technology provider, logistics operator, or consultancy firm, you are not merely sharing good news – you are handing attackers a detailed map of your extended attack surface.
Supply chain attacks have surged dramatically in recent years. Research indicates that 45% of organisations experienced at least one software supply chain attack in the past 12 months, and the trend is worsening. In 2024 alone, supply chain phishing attacks affected 183,000 customers – a 33% year-on-year increase. The SolarWinds breach, the Kaseya attack, and countless less-publicised incidents have followed the same fundamental playbook: identify a trusted third party, compromise them first, and exploit that trusted relationship as a bridge into the primary target.
When your LinkedIn company page announces a new partnership with a named supplier, threat actors note it. They research that supplier. They cross-reference the supplier’s own LinkedIn presence to identify who manages your account. They craft a spear-phishing email from a spoofed domain that mimics the supplier. Your finance team receives an urgent invoice change request, your IT team receives a convincing software update notification – and a sophisticated intrusion begins.
Hackers do not always break down the door. Often, they simply walk through it – dressed as someone you already trust.
On supply chain social engineering
The Social Engineering Escalation
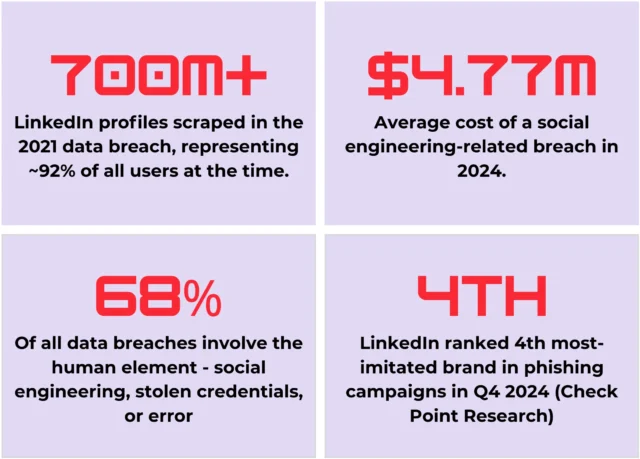
Social engineering – the art of manipulating people rather than systems – now accounts for 22% of all data breaches involving external threat actors, and it is becoming significantly more sophisticated with the advent of artificial intelligence. In 2024, vishing (voice phishing) attacks skyrocketed 442% between the first and second halves of the year, with attackers increasingly deploying AI-generated voice clones to impersonate executives and IT staff convincingly.
LinkedIn provides the intelligence layer that powers all of this. Before an attacker places a call, sends a message, or crafts a phishing email, they build a target profile. They know your job title, your team’s structure, your manager’s name, which projects you have just announced, and which vendors you work with. That profile – assembled largely from LinkedIn – transforms a generic phishing attempt into a targeted, contextually credible attack that even experienced professionals struggle to detect.
Consider the anatomy of a typical spear-phishing campaign informed by LinkedIn reconnaissance. The attacker identifies a junior accounts payable administrator from their public profile. They note the employee recently posted about joining the company. They identify the Finance Director from the company page. They observe a recently announced ERP system migration. Armed with this, they craft an urgent, personalised email appearing to come from the Finance Director, referencing the new ERP rollout, requesting the employee process a supplier payment. The email is plausible, contextually accurate, and deeply convincing. According to IBM research, the median time for a recipient to click a phishing link is just 21 seconds.
⚠ Intelligence Failure
Cybersecurity professionals – those whose explicit job function is to protect corporate data – routinely post about new security programmes, compliance projects, and risk initiatives on LinkedIn. This isn’t just ironic (to put it politely); it is operationally dangerous. Announcing a new endpoint security deployment, a penetration testing programme, or a supplier security audit publicly signals both the gaps that are being addressed and the timeline for doing so – handing adversaries a window of opportunity.
The Front Door Is Always Open
There is a principle in physical security: it is often easier to walk through the front door than to scale a wall. The same applies in cybersecurity. Organisations invest millions in perimeter defences, next-generation firewalls, endpoint detection, and zero-trust architecture – and then their employees voluntarily publish the equivalent of a building schematic to an audience of one billion people.
Low-level administrative users represent a particularly high-value target precisely because they frequently hold access to critical systems – HR platforms, financial software, cloud infrastructure, email – whilst receiving less security training and scrutiny than senior executives. Attackers know this. They actively seek these individuals on LinkedIn and target them with tailored approaches.
This is why a mature, layered cybersecurity programme is critical. Defence-in-depth means building multiple, overlapping controls so that no single point of failure – including human error – results in a catastrophic breach. Key technical controls in this architecture include:
- Device Control Policies – Preventing access to unapproved USB devices, a common vector in physical social engineering campaigns and insider threat scenarios.
→
- Data Classification & Loss Prevention – Automated policies that prevent the copying, transfer, or exfiltration of sensitive data, regardless of how access was obtained.
→
- Privileged Access Management (PAM) – Ensuring that administrative users operate with least-privilege access, minimising the blast radius of any compromise.
→
- Phishing-Resistant MFA – Moving beyond SMS-based authentication towards FIDO2 hardware keys or certificate-based authentication that cannot be bypassed by adversary-in-the-middle techniques.
→
- Continuous Security Awareness Training – Simulated phishing, vishing, and smishing exercises that build genuine human resilience – because 33% of employees across industries remain vulnerable to phishing at any given moment.
→
- Third-Party Risk Management – Rigorous vetting and ongoing monitoring of all suppliers and partners, treating their security posture as an extension of your own attack surface.
Your Data, Productised and Sold Back to You
There is a profound irony at the commercial heart of LinkedIn that deserves to be stated plainly. The personal and professional data you freely upload to the platform – your career history, your connections, your company’s organisational structure, your business relationships – is not merely stored. It is analysed, enriched, and packaged into products that are then sold back to you and to third parties, in the form of Sales Navigator subscriptions, premium memberships, and targeted advertising services.
LinkedIn’s own privacy policy confirms that your data may be used to infer attributes including industry, seniority level, compensation bracket, interests, and more – all for advertising and targeting purposes. Third-party advertisers are also permitted to track users both on and off the platform. Your data is shared with Microsoft’s broader ecosystem of services, and it feeds advertising targeting that you have not explicitly consented to in any granular sense.
The platform takes the security of its own systems seriously. What it demonstrably cannot – and will not – do is protect you from the consequences of the information you have chosen to share. In 2021, data pertaining to approximately 700 million LinkedIn accounts was scraped and made available for purchase on underground forums. LinkedIn’s response was that this constituted scraping of publicly available data rather than a breach of their systems – which is technically accurate, and entirely beside the point. Your data was harvested, packaged, and sold. The privacy watchdog of Italy – which has one of the largest LinkedIn user bases in Europe – launched an investigation immediately.
Furthermore, numerous countries and jurisdictions have taken the significant step of blocking LinkedIn entirely, citing precisely these concerns around data sovereignty, privacy, and the platform’s handling of user information. Russia imposed its block following LinkedIn’s refusal to store Russian user data on domestic servers. That regulatory action, whatever one may think of the broader political context, reflects a recognition that LinkedIn’s data practices represent a meaningful risk to citizens and organisations.
The Vanity Economy & the Spam Epidemic
Beyond the security dimension, there is a commercial reality about LinkedIn’s effectiveness that the platform’s marketing machine has successfully obscured. The click-through rate for LinkedIn sponsored content averages between 0.44% and 0.65% – poor by any standard. InMail response rates sit stubbornly in the low single digits. For organic outreach and prospecting, LinkedIn’s conversion performance is, in most contexts, strikingly modest relative to the time, money, and personal data invested.
The corollary is a platform saturated with unsolicited commercial outreach that borders on industrial-scale spam. The moment a business page is established on LinkedIn and linked to identifiable individuals (speaking from experience), the volume of unsolicited direct outreach – both through the platform and, crucially, to associated email addresses harvested from public profiles – increases dramatically. Documented experiments using honeypot business pages – fictitious profiles constructed specifically to measure this effect – have recorded between 80 and 100 unsolicited commercial emails per individual per day. Pivoting those pages to an ambiguous, low-signal presence produced a collapse in spam volume of approximately 95%. The correlation is direct and reproducible. It is also worth noting that much of this unsolicited commercial contact is a violation of anti-spam legislation in the United Kingdom, Australia, the European Union, and numerous other jurisdictions – yet the infrastructure enabling it is, effectively, monetised by the platform.
The social character of LinkedIn has also degraded considerably. What was once a professional network has, for many users, evolved into a platform characterised by performative self-promotion, politically charged opinion, and the relentless pursuit of engagement metrics for their own sake. The genuine knowledge-sharing and collaborative value that the platform once offered has been diluted by an attention economy that rewards volume, controversy, and personal brand-building over substantive professional discourse.
A Practical Recalibration
None of this is an argument for abandoning professional networking or digital presence management. It is an argument for deliberate, security-conscious boundaries. The next time you consider posting about a new team hire in your security operations centre, a recently signed technology partnership, an ongoing compliance project, or a new IT infrastructure initiative – pause and ask a simple question: Who else is reading this, and what can they do with it?
The answer, increasingly, includes some of the most sophisticated and patient threat actors on earth. Advanced Persistent Threat groups routinely spend weeks or months in the reconnaissance phase before a single line of malicious code is deployed. They are reading your company updates. They are cross-referencing your employee profiles. They are building a target dossier that your LinkedIn presence has made significantly easier to compile.
Removing this one, highly visible, voluntarily maintained attack vector will not eliminate the threat. But it meaningfully reduces the intelligence available to those who wish to exploit your organisation. In cybersecurity, friction matters. Every layer of complexity that an attacker must overcome increases the cost and risk of their operation – and increases the probability that they move on to an easier target.
The most effective security awareness programme in the world cannot compensate for an organisation that publicly broadcasts its own attack surface.
On the limits of reactive security
There are concrete, immediate steps any security-conscious organisation can take. Conduct a social media audit – review what your company pages, your leadership team, and your employees are collectively broadcasting to the world. Implement a social media security policy that explicitly addresses what may and may not be shared publicly regarding technology, partnerships, personnel, and security initiatives. Train your people not merely on phishing recognition, but on the broader discipline of information hygiene – understanding that the aggregate of innocuous-seeming public information creates a highly sensitive intelligence picture. Or, better yet, follow the lead of millions of global businesses and simply delete your LinkedIn business profile!
And for those whose professional vocation is cybersecurity, governance, risk, or compliance: the standard you hold your organisation to must first be applied to yourselves. Announcing publicly that your team is implementing a new SIEM platform, deploying a zero-trust network architecture, or preparing for an ISO 27001 audit does not demonstrate thought leadership. It demonstrates precisely the kind of operational security failure that makes the rest of your work significantly harder to sustain.
The Reconnaissance Is Already Under Way!
Every post, every partnership announcement, every new hire celebration is a data point in someone else’s attack playbook. The question is not whether hackers see your LinkedIn activity (because they do), the question is whether you’re going to make it easy for them.